Cyber Threat Guardian (CTG) is a multi-player card game, for ages five and up, that introduces players to technology and cybersecurity terms and concepts. See the About page.
Like other family games, it involves a little strategy and a bit of luck. This game provides a fun way for younger children to begin learning about patterns, online safety practices, technology terminology and cyber-safety!
CTG is also an easy card game for the classroom where students learn as they play. For more information on how to play, download the rulebook or watch a game in action.
Goal
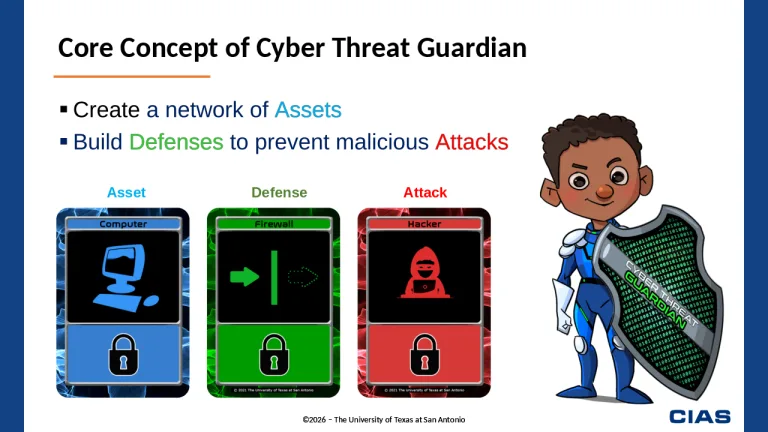
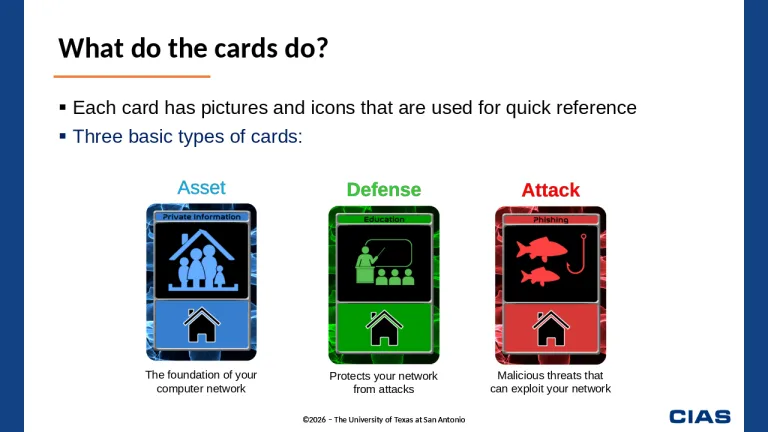
In Cyber Threat Guardian, the goal is to build a network and protect it from your opponent. While building up a network of assets, each player must also work to defend their network from their opponent’s attempts to disrupt their system from cyber threats. Players quickly learn that for every attack there is a specific defense. The player with the most complete set of security defenses will be the one to protect their critical systems and emerge victorious.
There are two primary objectives to consider when playing:
- Each player lays down as many blue asset cards as possible while protecting each asset with a green defense card.
- The player with the most asset and defense cards at the end of the game is the winner.
However, the rules and game setup vary for three different age groups: Grades K-1, Grades 1-2, and Second Grade and up. Choose the game option that best fits your needs.

Setup
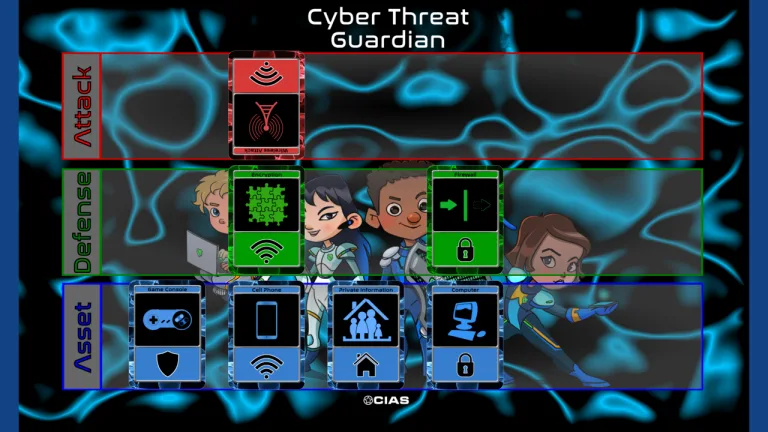
Regardless of the game option you choose, blue asset cards should be placed closest to the player. Green defense cards are place above the asset cards. Red attack cards are place above the defense cards. If players are using a CTG game mat, cards will be placed in their respective areas as identified on the mats.
Below is a sample layout of how cards should be placed. Note that the cards demonstrate how cards align with their icon categories, which supports game play for grades 1-2 and grades 2 and up.
Icon Categories
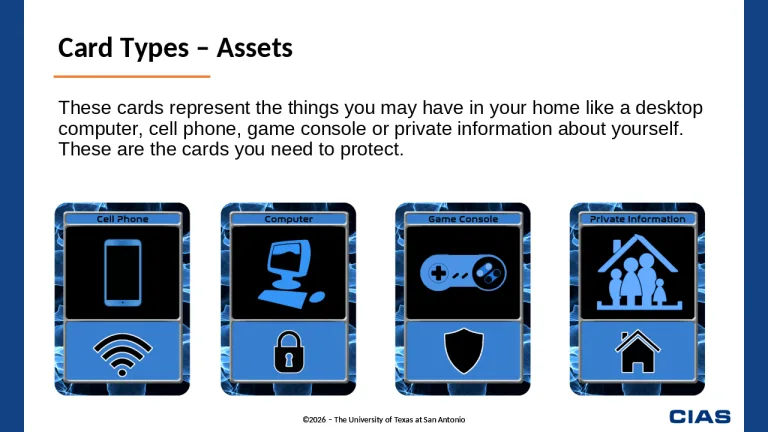
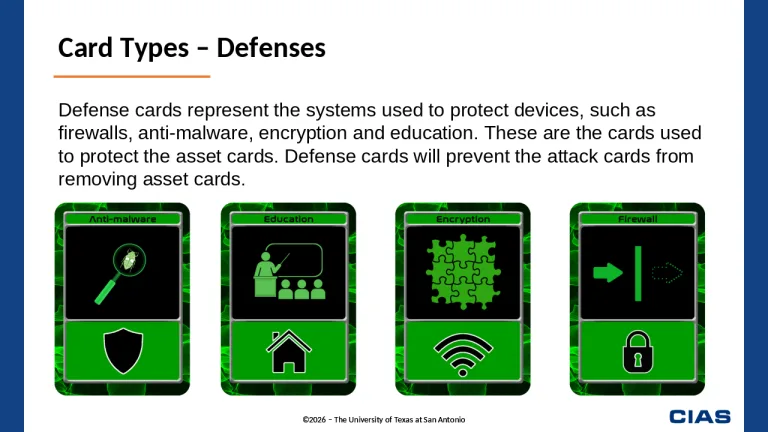
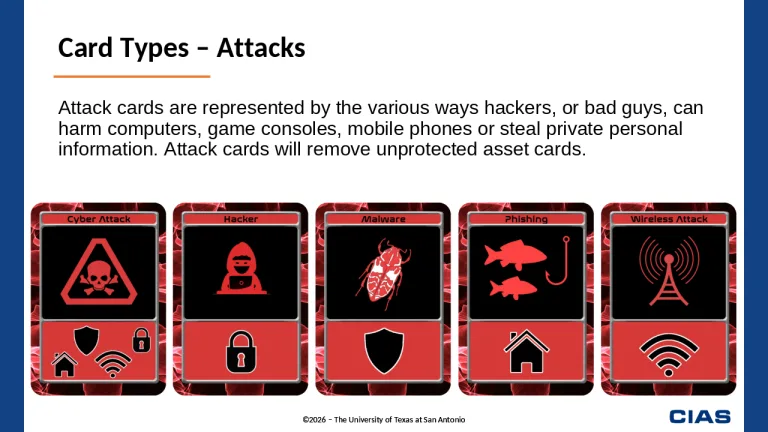
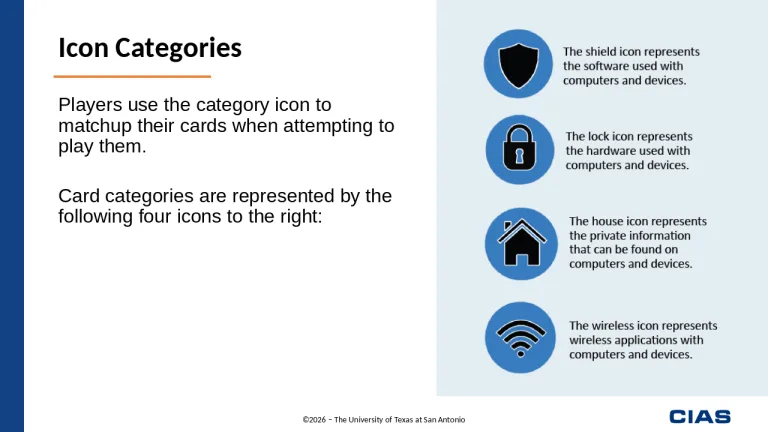
In Cyber Threat Guardian, there are four category icons. For grades 1 and up, players must use the icons to matchup their cards when attempting to play them. These categories are represented by the following four icons:

The house icon represents the private information that can be found on computers and devices.

The lock icon represents the hardware used with computers and devices.

The shield icon represents software used with computers and devices.

The wireless icon represents wireless applications with computers and devices.
How to play
The game setup and rules vary for three different age groups. Select the game option below that best fits your audience and/or interest. Enjoy!
NOTE: In this version of the standard game, players do NOT need to matchup category icons when playing their cards.
Step 1
Both players draw one card from the draw pile (it does not matter who draws first). Depending on the card, players can make one of the following moves:
- If the card is a blue asset card, the player places the card in front of them in the playing area next to their other asset card.
- If the card is a green defense card, the player places the card in front of any blue asset card that is in their playing area that does not already have a defense card protecting it.
- If the card is a red attack card, the player can use it to remove any unprotected blue asset card of their opponent. (i.e., there is no defense card in front of the asset card).
- If the player is unable to make any of the above moves, the card is placed in the discard pile.
Note: Cards are played in the following order: blue asset cards, green defense cards and then red attack cards.
- (Example one) If Player 1 draws a blue asset card and Player 2 draws a green defense card, then player 1 places their asset card in front of him and then player 2 places their defense card above any of their unprotected blue asset card with the same category icon that they may have.
- (Example two) If Player 1 draws a red attack card and Player 2 draws a green defense card, then Player 2 places their defense card first above any unprotected asset card (remember to play in order of asset, defense and then attack cards). Player 1 then can use their attack card to remove any unprotected asset card of their opponent.
Step 2
Play continues with each turn; both players drawing one card and attempting to play that card as described in Step 1 above.
Step 3
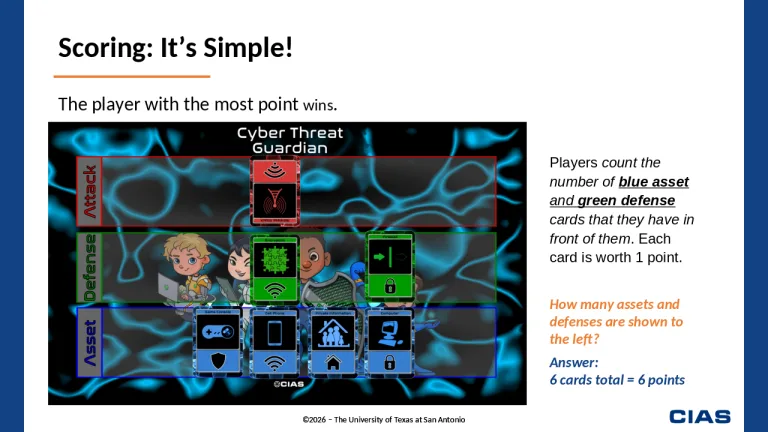
Once the players use all the cards in the draw pile, the game ends. Players will then count the number of blue asset and green defense cards that they have in front of them. Each card is worth 1 point. The Player with the most points wins the game.
NOTE: In this version of the standard game, players must use the category icon to matchup their cards when attempting to play them.
GAME SETUP
A. Each player selects one blue asset card and places it in front of them in the playing area.
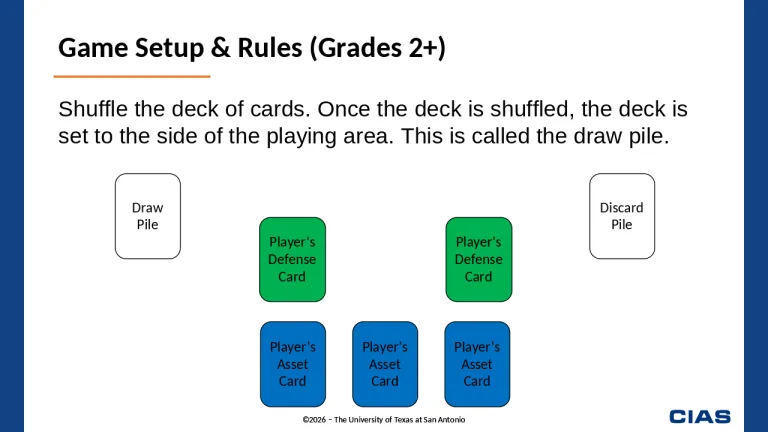
B. Shuffle the cards. Once the deck is shuffled, the deck is set to the side of the playing area. This is called the draw pile.
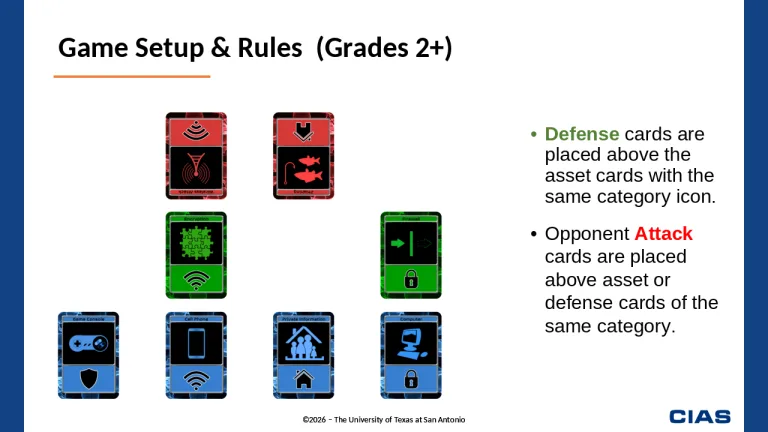
C. Asset Cards are placed closest to the player. Defense cards are placed above the asset cards with the same category icon. Attack cards are placed above asset or defense cards of the same category.
GAME PLAY
Step 1
Both players draw one card from the draw pile (it does not matter who draws first). Depending on the color of the card, players can make one of the following moves:
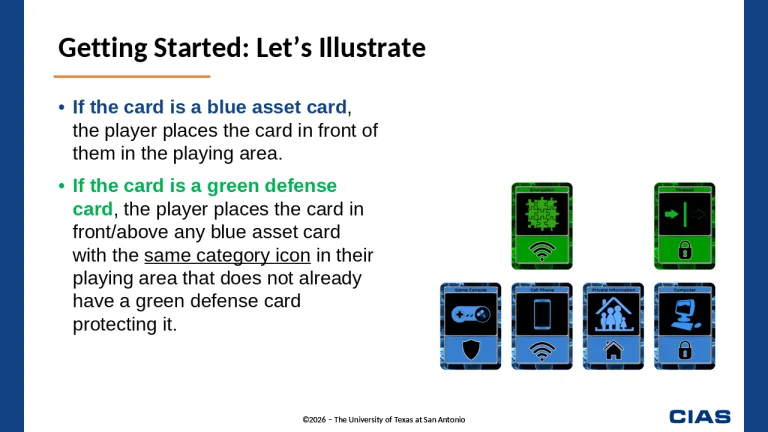
- If the card is a blue asset card, the player places the card in front of them in the playing area next to their other asset cards.
- If the card is a green defense card, the player places the defense card in front of any blue asset card with the same category icon that is in their playing area. The defense card can be played only if the blue asset card does not already have a green defense card protecting it.
- If the card is a red attack card, the player can use it to remove any unprotected (there is no green defense card in front of the blue asset card) asset card of their opponent with the same category icon.
- If the player is unable to make any of the above moves, they discard the card and place in the discard pile.
Note: Cards are played in the following order: blue asset cards, green defense cards, and then red attack cards.
- (Example one) If Player 1 draws a blue asset card and Player 2 draws a green asset card, then player 1 places his card in front of him and then player 2 places his green defense card above any unprotected blue asset card with the same category icon that they may have.
- (Example two) If Player 1 draws a red attack card and Player 2 draws a green defense card, then Player 2 places his green defense card first above any unprotected asset card. Player 1 then can use their red attack card to remove any unprotected asset card with the same category icon of their opponent.
Step 2
Play continues with each turn, both players drawing one card and attempting to play that card as above.
Step 3
Once the players use all the cards in the draw pile, the game ends. Players will then count the number of blue asset and green defense cards that they have in front of them. Each card is worth 1 point. The Player with the most points wins the game.
NOTE: In this version of the standard game, players must use the category icon to matchup their cards when attempting to play them.
GAME SETUP
A. Each player begins this version of the game without any blue asset card in front of them in the playing area at the start of the game.
B. Shuffle the cards. Once the deck is shuffled, the deck is set to the side of the playing area. This is called the draw pile.
C. Asset Cards are placed closest to the player. Defense cards are placed above the asset cards with the same category icon. Attack cards are placed above asset or defense cards of the same category.
D. The red attack card with the four category icons can be used to remove any of the green defense or blue asset cards.
GAME PLAY
Step 1
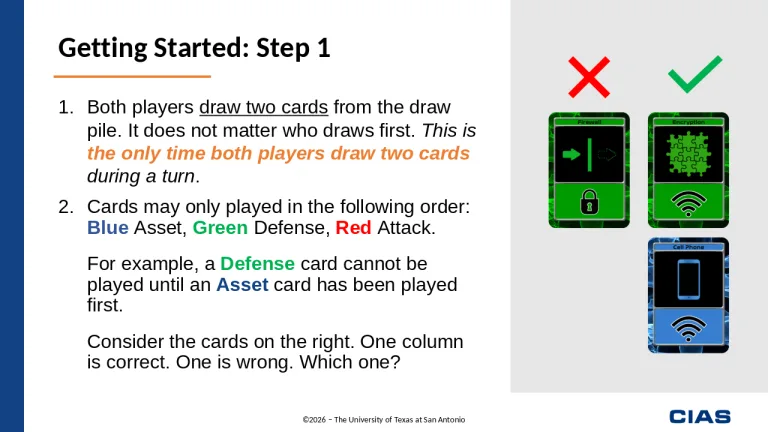
Both players draw two cards from the draw pile (it does not matter who draws first). Depending on the color of the card, players can make the following moves:
- If the card is a blue asset card, the player places the card in front of them in the playing area.
- If the card is a green defense card, the player places the card in front of any blue asset card with the same category icon that is in their playing area that does not already have a green defense card protecting it.
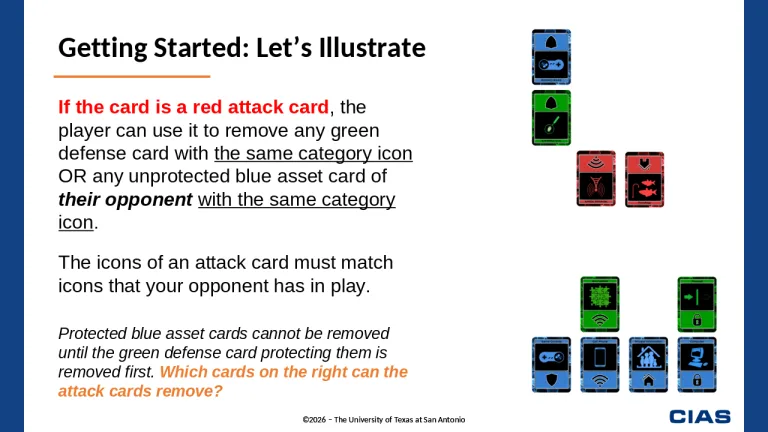
- If the card is a red attack card, the player can use it to remove any green defense card with the same category icon OR any unprotected blue asset card of their opponent with the same category icon. Protected blue asset cards cannot be removed until the green defense card protecting them is removed first.
- If the player is unable to make any of the above moves, they discard the card and place in the discard pile.
Note: Cards are played in the following order: blue asset cards, green defense cards and then red attack cards.
- (Example one): If Player 1 draws a blue asset card and Player 2 draws a green asset card, then player 1 places his card in front of him and then player 2 places his defense card above any unprotected asset card that they may have.
- (Example two): If Player 1 draws a red attack card and Player 2 draws a green defense card, then Player 2 places his defense card first above any unprotected asset card. Player 1 then can use their red attack card to remove any green defense card or unprotected blue asset card with the with the same category icon.
Step 2
Play continues with each turn, both players drawing one card and attempting to play that card as above.
Step 3
Once the players use all the cards in the draw pile, the game ends. Players will then count the number of asset and defense cards that they have in front of them. Each card is worth 1 point. The Player with the most points wins the game.
Note to Security Professionals
In developing this game, we recognize that we have taken some liberties with how things actually work. We have attempted to keep true to the spirit of computer security, but for playability reasons have slightly modified how things might actually work in reality. We believe, however, that the game is close enough that individuals playing the game will be able to gain some understanding of basic computer security concepts.