About
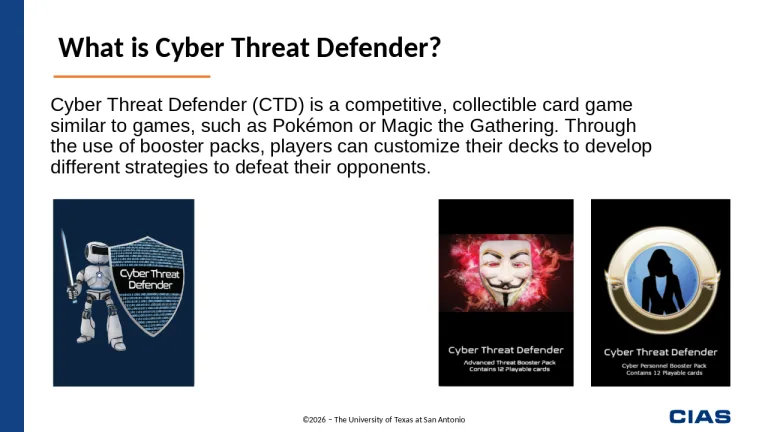
Cyber Threat Defender is designed as a two-player game, but it can be modified to allow for more players. Below is a brief overview to help you get started.
For more detailed instructions, including an example of a sample round of play, download the Cyber Threat Defender Rulebook or watch our video tutorials on how to play below.
Goal
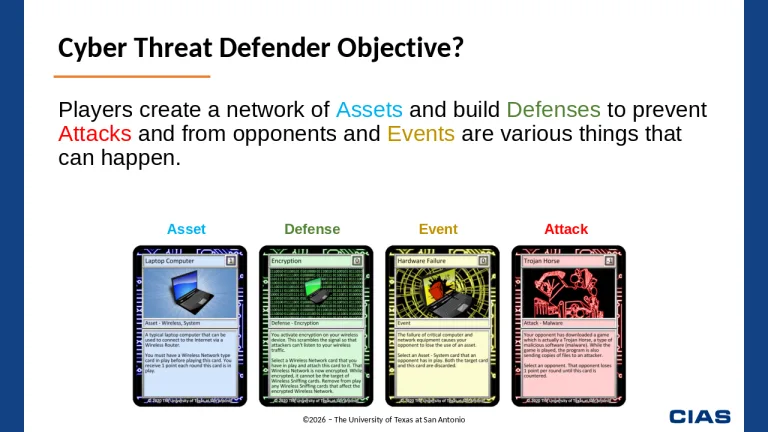
The goal of Cyber Threat Defender (CTD) is to securely increase the size of your network. The more robust your network (or number of asset cards), the more points a player earns each turn. The first player to reach 30 points wins the game.
A player can also customize their Starter Decks by incorporating booster packs into their deck. These booster cards can further hinder an opponent’s ability to build their network while creating new opportunities to build your own network.
FAQ
Is there a maximum number of cards allowed in my personal Cyber Threat Defender deck?
No, there is no maximum number of cards. You may customize your deck by adding as many booster cards to your starter deck as you want.
Can I stack (duplicate) defenses?
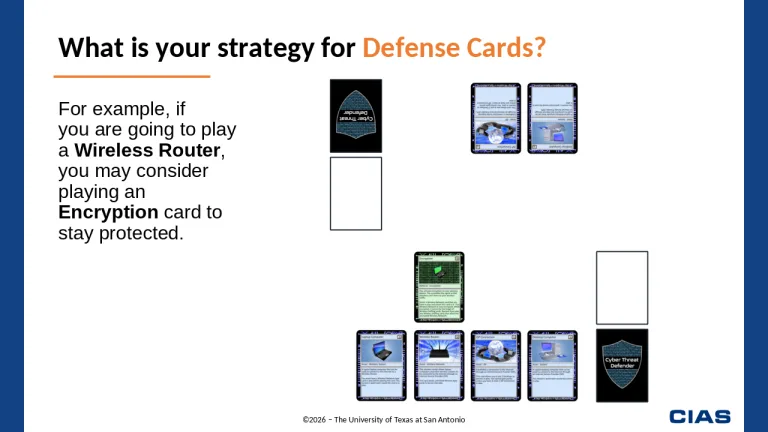
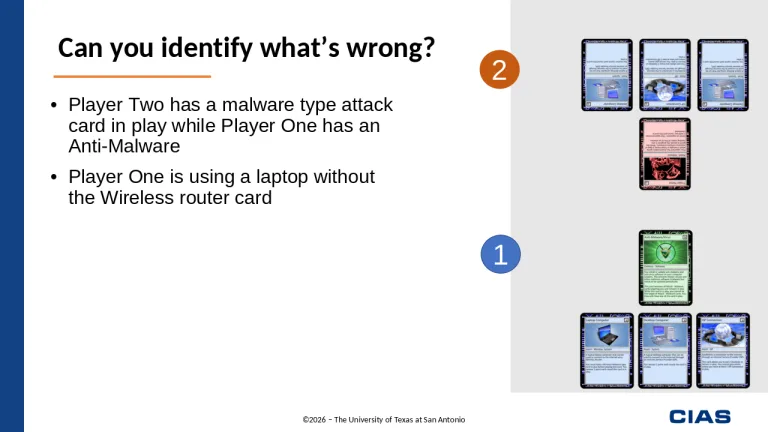
No. You cannot have duplicate defenses in play at a time. For game purposes, only one of each defense card can be played at a time to ensure cards remain balanced throughout the game when playing against attack cards.
Can I stack (duplicate) attack cards?
Yes, unless an attack card specifically states only one of its kind may be in play at a time. Similar to the real world, a computer system may be targeted by cyber-attacks from multiple sources. For example, various bad actors (hackers) may be targeting your computer system with the same or similar types of attacks.
How do I remove a specific card from an opponent’s play field?
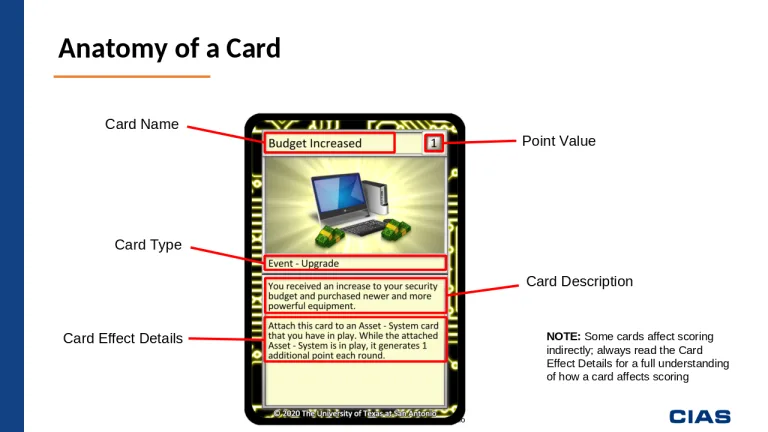
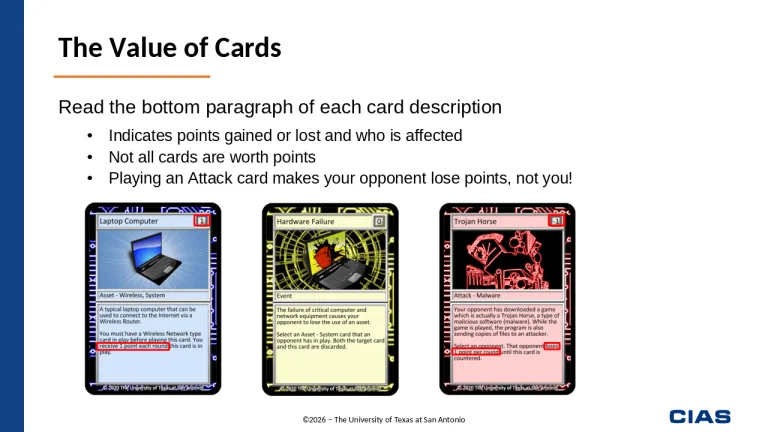
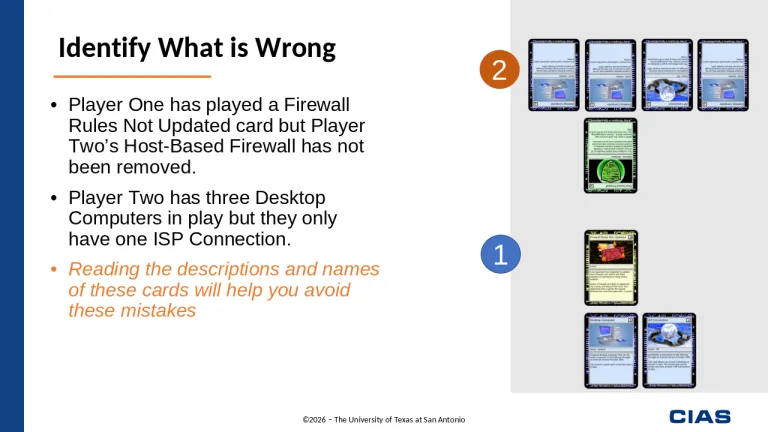
The second paragraph on the bottom of each card explains how that card interacts with other cards. For example, an attack card will state which specific types of defense cards it can remove. Pay attention to the rules on each card – some card rules may allow you to randomly select a card from an opponent’s hand if a specific card is not already on the opponent’s play field.
How do I know if my attack and/or defense card can counter my opponent’s cards?
Each card states, whether an Event, Defense or Attack card, what cards it can counter against. Pay attention to both your cards and your opponent’s cards to ensure the appropriate cards are being removed when countered and that they are (potentially) removed after a specific number of turns. The second paragraph of each card will explain if the card can counter an opponent’s cards.
How many cards must I draw when my turn ends?
Each player is required to draw two cards at the end of every turn. Keep in mind that each player can have no more than seven cards in their hand at the end of each turn. For example, if a player has only three cards left when finishing their turn, that player will then draw two cards, which means the player completes their turn with five cards total. However, if a player ends a turn with six cards, they must discard one card of their choice and then draw two cards. This will leave the player with seven cards at the end of their turn.
Can one CTD Starter Deck be shared between two players?
Yes. While the Cyber Threat Defender game is designed for each player to have their own personal deck, a single deck can be shared between two players. If this happens, the two players can either randomly distribute or remove one copy of each of the following cards: Desktop Computer, Laptop Computer, OS Update/Patch, Poor Encryption Key, and Security Training.
Once those cards are distributed, shuffle the deck and split evenly between the players.
What happens if my turn is skipped, such as when my opponent plays a Power Outage card?
If your turn is skipped, or a card states you do not receive any point during the round/turn, you do not receive any points for assets that you own during the round.
Where can I purchase additional cards?
Cyber Threat Defender starter decks, booster packs, game mats and rulebooks can be purchased through our online store: CIAS.store.
How to play CTD






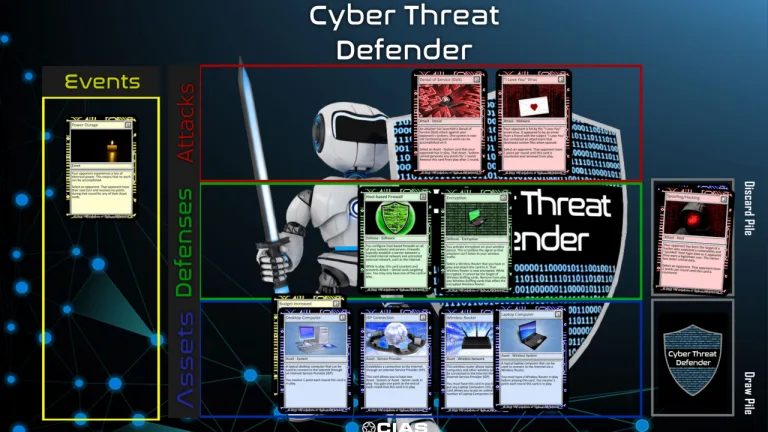
Setup
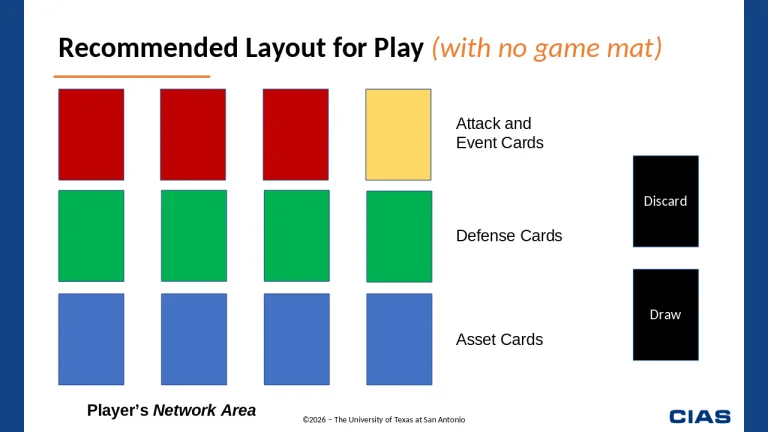
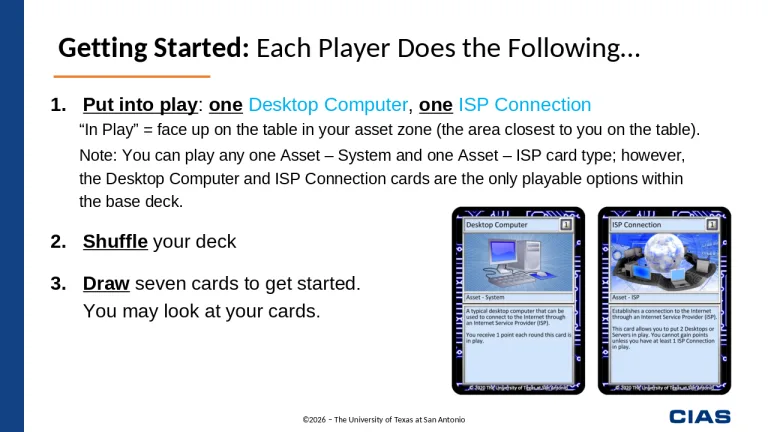
Each player needs to go through their deck and place one Asset – System (Desktop Computer card) and one Asset – ISP (ISP Connection card) face up in their play field. These two cards are required to “start” their network.
Once the two cards are placed on the table, each player needs to shuffle their decks and place the deck face down as their Draw Pile. Leave space next to the Draw Pile for a Discard Pile when cards are discarded. Each player can then draw seven cards from the top of their draw pile and look at their cards. Do not show the opponent your cards.
Now, decide which player goes first. This turn order will remain the same for every round of play.

Gameplay
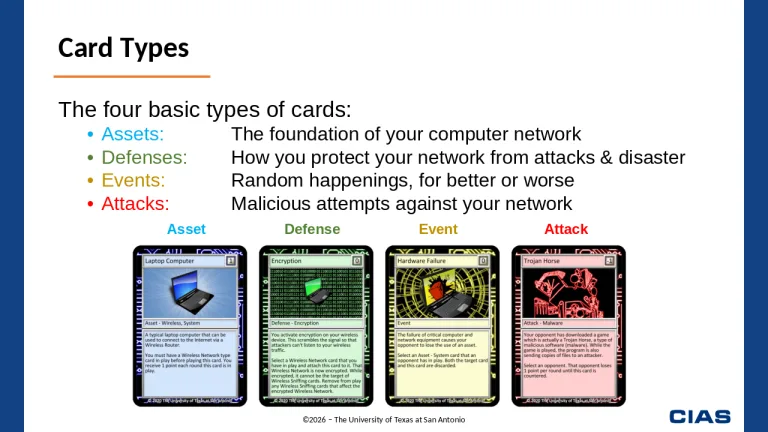
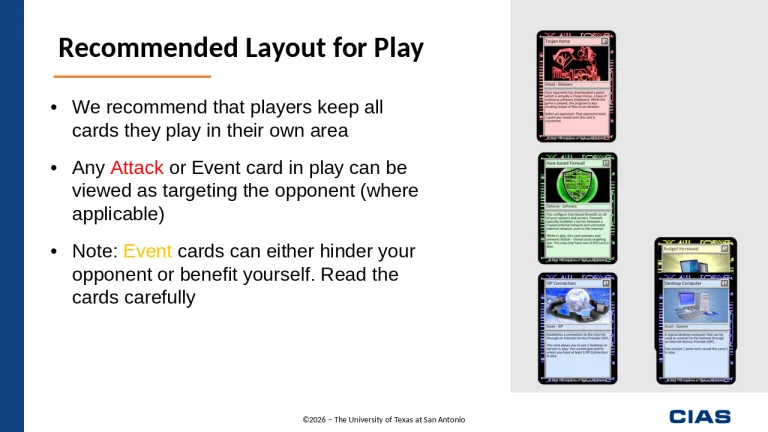
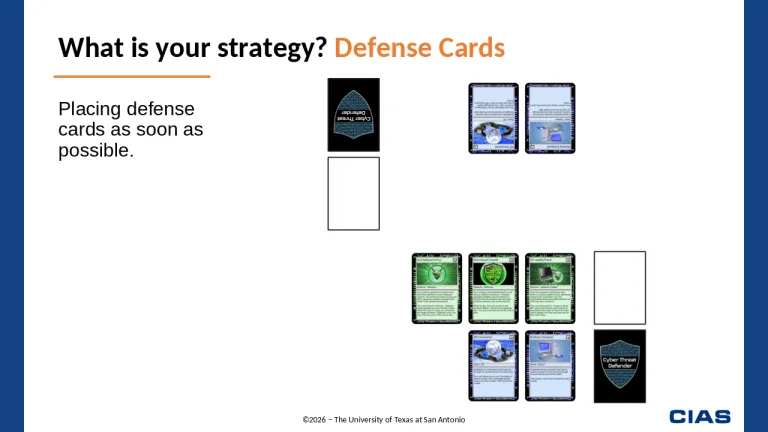
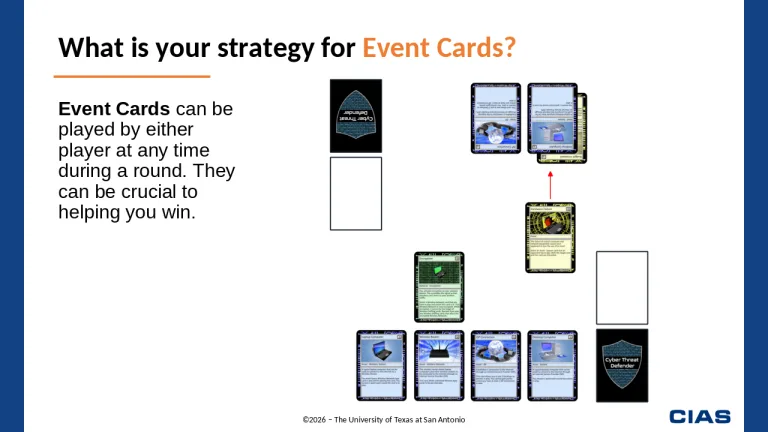
A round of play consists of one turn for each player. A player can play up to three cards during their turn, with the exception of an Event card. Event cards can be played at any time during a round, regardless of the player’s turn, and does not count toward their three-card limit.
At the end of a player’s turn, if that player has more than five cards in their hand, they must discard cards from their hand until they have exactly five cards.
Once the player has five or fewer cards in their hand, then they must draw two cards from their Draw Pile. This signifies the end of their turn and the second player can now play their cards. Scores are tallied at the end of a round.
For an example of a round of play, download the CTD Rulebook or watch the video below on a full game being played.
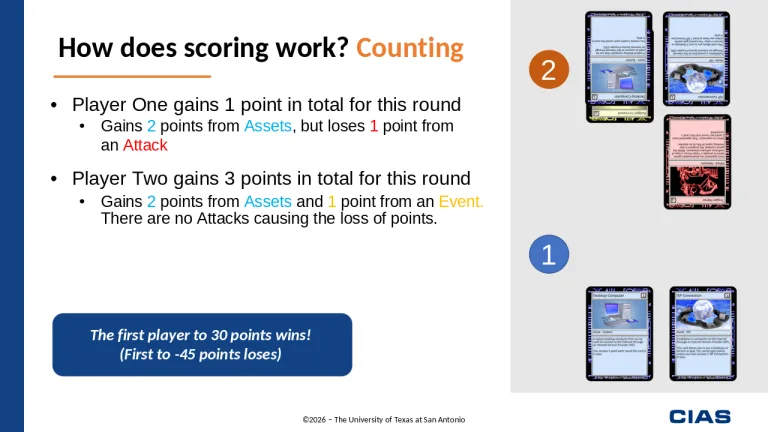
Scoring
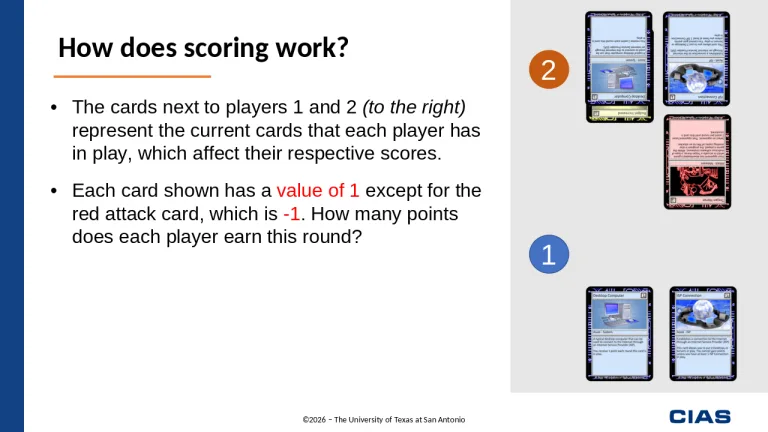
Keep track of the points identified on each card. Only Asset cards provide opportunities for a player to gain points; however, both Event and Attack cards may be able to remove points from an opponent’s field.
With this in mind, at the end of each round, both players need to tally their points gained from Assets in their play field and subtract points played against them from their opponent’s Attack cards.
Winning
Players should be keeping score at the end of each round. If one player accumulates 30 or more points and has more points than their opponent, they are the winner; otherwise, play continues until there is a winner.
Losing
- If a player must draw a card but their Draw Pile is empty, they lose the game.
- The first player to -45 points loses the game.
My students love playing Cyber Threat Defender. We use it in my computer repair course, and it is really the only exposure to security they get. I find that as they continue to play the game and get used to the available cards, they are also getting a basic understanding of the different threats and security features that are out there. They also start getting a good idea of the need for different layers of defence to combat different types of attacks. Sometimes I have students in different courses later on (after they have taken the computer repair course) and they all ask if they will get to play the game again.
Jason Smith, Computer Science Teacher
Note to Security Professionals
In developing this game, we recognize that we have taken some liberties with how things actually work. We have attempted to keep true to the spirit of computer security, but optimized the game for playability rather than a perfect match to reality. We believe, however, that the game is close enough that unfamiliar players will be able to gain some understanding of basic computer security concepts.